Folio3 User Security Reports developed for Microsoft Dynamics AX 2009 & AX 2012 R1, R2 & R3 are designed to help customers and partners who are looking for a comprehensive security report detailing out the information on users, their roles, assigned duties or tasks and other relevant information. Security Auditors can leverage our reports to review how security has been implemented in in Microsoft Dynamics AX implementation using out of the box security framework.
It is very important to understand how securable objects work in AX and are related to specific privileges, through duties and roles. We can help you manage these better and also leverage Microsoft’s out-of-the-box features to boost your internal AX security. Our team of AX security experts clearly understands the security options available for each element of Dynamics AX, be it out-of-the-box or custom.
To setup a fool proof Security architecture for Dynamics AX, it is important to understand the role based security model introduced with AX 2012 and the security domains framework that was present in earlier versions of AX 2009 and 4.0.
Get in touch with us today to optimize your Dynamics AX Security parameters.
Role-based security brings a lot of new scope possibilities such as segregation of duty, rule based-date effective assignment of privileges etc. It is important to consider security implications during the customizations and gap scoping that goes on during the discovery phase of a project. Now more so then ever, security has a larger impact on design time, for when implementing Dynamics AX.
Increasingly, AX security is being looked at from a functional level as role-based security has impacted the functional design and the nature of AX implementation projects.
Our Dynamics AX team deeply looks into the security architecture and design of your ERP environment and recommends improvements to ensure that you are maximizing on your ROI.
Get in touch with us today to optimize your Dynamics AX Security parameters.
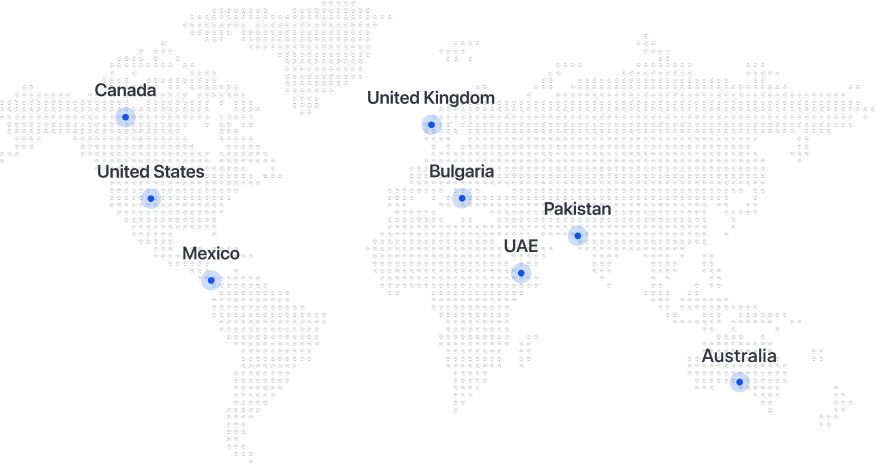

Folio3 Dynamics is specialized division of Folio3 that specializes in broad spectrum services around Microsoft Dynamics ERP stack.
160 Bovet Road, Suite # 101
San Mateo, CA 94402 USA
Ph: +1 408 365-4638
Email: [email protected]



Cookie Policy | Privacy Policy